What is an Account Lockout Policy?
An account lockout policy is a built-in security policy that allows administrators to determine when and for how long a user account should be locked out. It determines what happens when a user enters a wrong password. It ensures that an attacker can’t use a brute force attack or dictionary attack to guess and crack the user’s password. This can be configured from the local security policy of the computer or in the Group Policy Management Console by the network administrator.
How to Change the Account Lockout Policy in Active Directory
To edit and change the Account Lockout Policy settings, do the following:
- Go to Start Menu → Administrative Tools → Group Policy Management
- In the console tree, expand the Forest and then Domains. Select the domain for which the Account policies have to be set
- Double-click the domain to reveal the GPOs linked to the domain.
- Right-click Default Domain Policy and select Edit. A Group Policy Editor console will open.
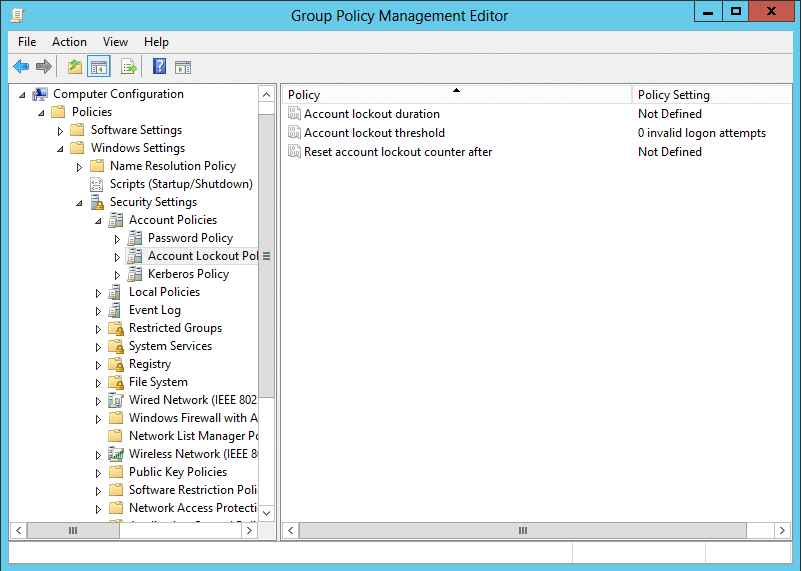
- Now, navigate to Computer Configuration → Policies → Windows Settings → Security Settings → Account Policies → Account Lockout Policy
- Double-click Account Lockout Policy to reveal the three account lockout settings available in AD. Right-click any one of these settings and select Properties to define the policy setting.
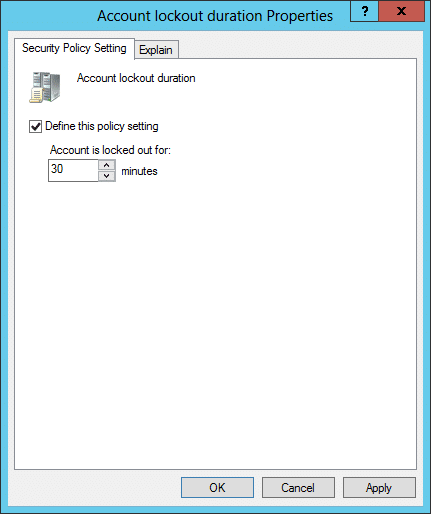
- The Properties dialog box of each policy setting will have two tabs. The Security Policy Setting tab is where the value for that setting is set. The Explain tab gives a brief description of the policy-setting and its default values
- In the Security Policy Setting tab, check the Define this Policy Setting check box and enter the desired value. Click Apply and then OK
The three settings available under the Account Lockout Policy:
Account Lockout Duration
This security setting determines the number of minutes a locked-out account remains locked out before it gets automatically unlocked. The value can be set between 0 minutes and 99,999 minutes. This setting needs the Account Lockout Threshold setting to be defined.
If the value is set to 0, then the account will not be unlocked automatically. The administrator has to unlock the account explicitly. By default, this setting is disabled. To unlock the account:
- In ADUC, right-click the user whose account is locked out and select Properties
- Under the Account tab of the user properties, check the Unlock Account checkbox to unlock the account
Account Lockout Threshold
This security setting determines the number of failed logon attempts that are allowed before a user account is locked out.
For example, if an attacker enters a wrong password for the first time, the badPwdCount attribute of the user object is set to 1. When the attacker continues to enter wrong passwords, the badPwdCount is incremented by 1 until it reaches the account lockout threshold value at which time the account gets locked. A locked-out account cannot be used to log on until the account lockout duration expires or an administrator explicitly unlocks the account.
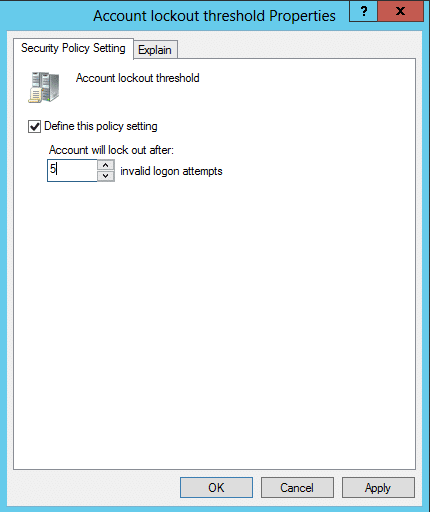
The value can be set between 0 and 999. If the value is set to 0, then the account will never get locked out. The default value is 0.
Reset Account Lock-out Counter After
This security setting determines the number of minutes that should elapse, after a failed logon attempt, for the failed logon counter to be set as 0. The value can be set between 1 and 99,999 minutes. This setting needs the Account Lockout Threshold setting to be defined.
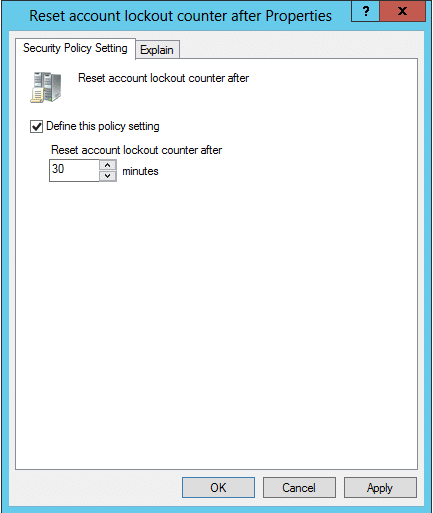
If the Account Lockout Threshold is defined, then the Reset Account Lock-out Counter After value must be less than or equal to the Lockout Threshold duration.
Account lockout policy best practices
Setting the account lockout policies must be done with the utmost care. Ideally, an optimum value for each policy should be defined in order to strike a good balance between security and convenience. Here are values that you could follow:
- Account lockout threshold value set to to 20.
- Account lockout duration value set to 15 minutes.
- Password policy to require all users to have at least 8 characters.
- Reset account lockout counter after value set to 30 minutes.
People also read
Active Directory Password Policy






