What you will learn:
Managing an Active Directory (AD) network can become a little cumbersome once the number of resources in the network becomes larger. There is a myriad of things that need to be controlled such as security permissions, software installation, desktop settings for users and computers, administrator privileges, and many more. Group Policies make managing all these settings easier in the AD network. In this article, we will look at what AD group policies are, what are its types are, and how you can implement the group policies. We will also touch upon backing up group policies or forcing a group policy update.
What is Active Directory Group Policy?
AD Group Policies are critical pieces of instructions in an AD environment that an IT administrator can configure. AD group policies will determine the behavior and privileges for users and computers. Group Policies are primarily a security solution for the AD network. Administrators can configure these settings and then implement sets of these settings on sites, domains, or OUs containing users and computers.
What is a Group Policy Object?
Multiple group policy settings are bundled together in a set called a Group Policy object (GPO). Once an administrator configures the Group Policies in the GPO as necessary, he/she can then link the GPO to the container objects. The objects within the containers in question will then act within the boundaries and rules set by the policies in the GPO it was assigned. GPOs can be created and managed using the Group Policy Management Console (GPMC).
AD Group Policy precedence
When objects are placed within other objects, the child objects can inherit the Group Policy configurations of its parent container. This can also lead to an object being associated with multiple Group Policies. In such cases, the Group Policy precedence is as follows:
- GPO linked to the OU takes the highest precedence and is processed first
- This is followed by the GPO linked to the domain
- The GPO linked to the site takes third highest precedence
- Finally, the local Group Policy is processed and takes the lease precedence.
What are the benefits of Active Directory Group Policies?
There are several reasons why group policies are necessary for an organization. Here are some of them:
Uniform user experience
Users are no longer confined to a single computer in their workplace. They use different computers for different tasks. So, all their files and folders along with their personalized settings such as taskbar location, wallpaper settings, desktop icons, and more have to be made available in all the machines the user logs on to.
Security
Even with all the authentication protocols and authorization techniques involved in AD, a malicious user can still gain access to network resources if he/she gets to know a user’s password. So, it is extremely important to have a strong password set for all the users in an organization. It is also important to record certain events like user log in, access to a particular folder, and more for auditing purposes.
Organization-wide Policies
Most organizations use wallpapers, screen savers, interactive logon messages, and more in an effort to establish a standard among all their employees. Organizations also have Internet policies that all users in the organization should adhere to.
Cost and Time
Tasks like software installation consume a lot of time. Installing and updating software on all computers, for all users, will not only take time but also affect productivity, as employees will not have access to their computers when the installation is taking place.
Group Policies play a crucial role in ensuring that the employees of an organization can have a hassle-free experience when it comes to using the IT resources to accomplish their tasks.
Types of Group Policies in AD
There are two types of Group Policies in AD, which are:
- Local Group Policy
- Non-local Group Policy
Local Group Policy
Each computer running the windows line of the operating system has exactly one local group policy. It is available only to the particular computer in which it resides and the users who log on to that computer. The local group policy objects reside in the %systemroot%\System32\Group Policy folder. The local Group Policy settings only contain a subset of the entire settings available in the centralized Group Policy settings.
Centralized Group Policy
Each domain controller has one or more centralized group policies. They are available to all the machines and users in the AD environment. A centralized Group Policy can be applied to all users and computers in a domain, or to a particular OU depending on where the Group Policy is linked.
How to manage Group Policies in AD
AD Group Policies are managed using the Group Policy Management Console (GPMC). This is a snap-in that comes built-in since Windows Server 2008. The GPMC allows you to create GPOs, and link them to domains, sites, or OUs as necessary. For example, if you want to link a GPO to an OU or a domain, here’s how you can do it:
- Go to Start, and navigate to Administrative tools. Then, navigate to Group Policy Management and click on it.
- Click on a domain or an OU that you want to view.
- In the tabs available on the right side of the console, click on Linked Group Policy Objects tab.
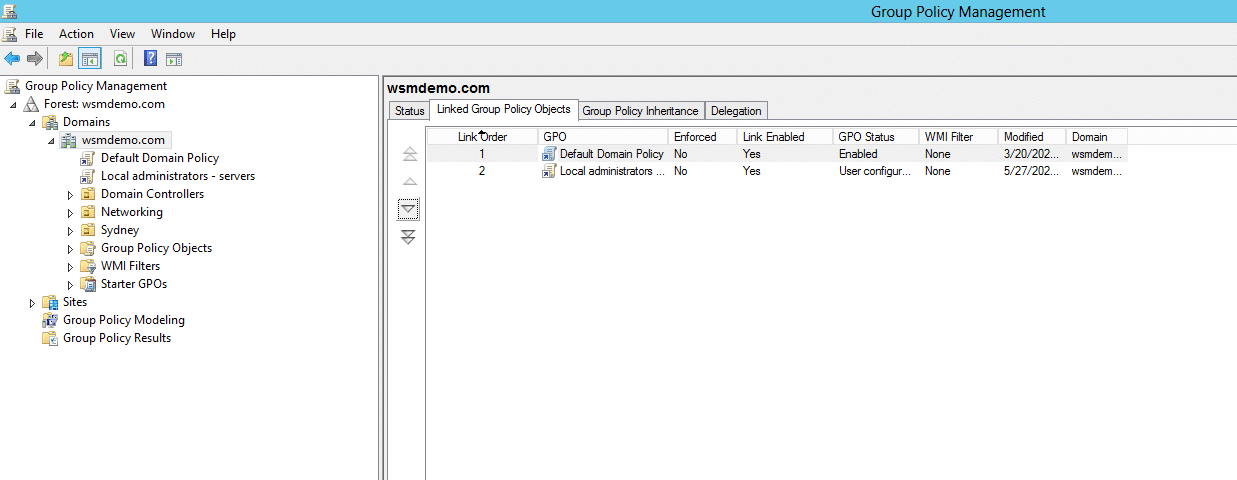
You will be able to see all the GPOs that are linked to the selected domain or OU. From here, you can manage the GPOs linked to the domain or OU.
Backing up Group policies in AD
Since GPOs are so critical in maintaining the organization’s security, it becomes necessary to backup GPOs should something unwarranted happen. There may be instances where two different administrators could implement two different GPOs to the same group, and that could potentially result in members of that particular group gaining access to resources that they don’t need or not get access to critical resources they need. In such cases, one administrator can restore GPOs from backups created earlier. There could also be instances where GPOs could be accidentally deleted or corrupted. In such cases too, having a GPO backup can ensure that the GPOs can be restored to their original working conditions. You can learn more about AD Group Policy backup in this article.
Forcing a group policy update
Active Directory does have a default schedule that runs when a group update takes place. By default, a group policy update takes between 90 and 120 minutes since updating the group policies. However, if you cannot wait that long for some specified reason, you would have to resort to the “force the GPO” update process.
There can be various reasons to force update a group policy. Perhaps there a critical policy setting has been overlooked, and the policy update has to be implemented as soon as possible. Perhaps during there was a restructuring process in an organization, resulting in the policies being updated, and maybe these policies are to come into effect immediately.
Group policies are also refreshed when users log off and log back on, but you cannot ask every user to log off and then log on again. In such scenarios, forcing group policy updates can help achieve the task of refreshing group policies immediately. To learn how you can force a Group Policy update, check this article.
People also read






