What is Active Directory Rights Management Services?
Sensitive information in an Active Directory environment can cause a great deal of trouble if it reaches the wrong hands. Every organization should do all in its power to avoid such a situation. Active Directory Rights Management Services (AD RMS) is a server role in Windows Active Directory, which aims to do just that. It has its own set of tools to help organizations work with security technologies and manage the rights on an organization’s intellectual property (that includes email messages, Microsoft Office documents, project information, contacts, etc.).
NTFS too can be used to specify access permissions on files and folders. However, NTFS permissions do not work outside the domain network, meaning no protection is offered to an organization’s information that is taken offsite. What makes it different from NTFS is that AD RMS has usage policies that follow the document wherever they are moved to. It also specifies a time period during which users can exercise control over the documents and perform actions such as modify, forward or print. Following its expiration, the documents become inaccessible to users. Note that even if a user gets full access through NTFS and only read-only permission through AD RMS, then the policies set by AD RMS holds. Tip: If you are interested on how to change the NTFS and share permissions, follow the embedded link.
AD RMS usage policy templates are customizable to suit the organization’s needs. For example, a template for a piece of confidential information may allow users to just view the content and not more. A template for the information that has to be renewed periodically, can set an expiry date or validity period on the content. All such templates are stored in the configuration database.
AD RMS features are fully integrated into the Microsoft Office Suite. They can be extended to work with third-party applications using appropriate AD RMS Software Development Kits (SDKs), or other servers in a domain if they are AD RMS enabled.
What constitutes an AD RMS system?
It works on the basis of client-server interaction. To get the service up and running, the following are required:
- A Windows server that runs the AD RMS role. It takes care of licensing and handling certificates, and manages users, applications, and settings relevant to content access policies.
- A Windows AD RMS client. It takes care of encrypting and decrypting data in addition to acquiring licenses and certificates from the above-mentioned server.
- A database server such as a Microsoft SQL server that stores all information about the usage policies.
How does AD RMS work?
The information that is to be protected is encrypted by AD RMS and stored in the AD RMS server. A user will be able to read or access the encrypted file only if he/she possesses the encryption key to decrypt this information. If a user is privileged to access the information, he/she will automatically be able to retrieve the key from the server and open the file. Even if the AD RMS-protected document is taken offsite, the user would need to contact the RMS server to retrieve the key.
As already mentioned, the Active Directory Rights Management Services limits access to files or emails with the help of various certificates and licenses. The following are some of them:
- Server Licensor Certificate (SLC) contains the public key that encrypts the content key in a publishing license and allows the server to extract the content key and issue End User Licenses (EULs) against the publishing key.
- Rights Account Certificate (RAC) is issued when a user tries to access an AD RMS-protected content for the first time. The RAC helps to identify specific users.
- Client Licensor Certificate (CLC) allows a user to publish AD RMS-protected content to the client computer. The CLC public key encrypts the content key and includes it in the publishing license that it issues. CLCs are specific to a user’s RAC.
- Publishing License determines the rights applied to an AD RMS-protected content. It contains the content key, which is encrypted using the public key of the licensing service. It also has the URL and the digital signature of the AD RMS server.
- End User License (EUL) is needed to access the AD RMS-protected content. Every document is issued an EUL by the server.
Consider the scenario where an author creates a document using Microsoft Word, which is AD RMS-aware. The author configures rights protection for the document and receives the Client Licensor Certificate (CLC) from the RMS server, and imposes usage rights on the document. The application, Microsoft Word in this case, encrypts the document with a content key. The content key is in turn encrypted with the RMS server public key. The server thus creates and issues the publishing license. Following these, the AD RMS-protected content is up on the file server, ready to be accessed. Assume that a user with a Rights Account Certificate (RAC) tries to open the document. The protected document, with the help of the RMS server, verifies if the user is authorized to access it. When the server confirms that the recipient is authorized, it issues the End User License (EUL). The default validity period of this license is thirty days. The client now decrypts the content key using the public key it was issued. The user can consume the document.
Installing Active Directory Rights Management Services
The following steps illustrate how to perform the installation:
- Go to Start Menu → Administrative Tools → Server Manager
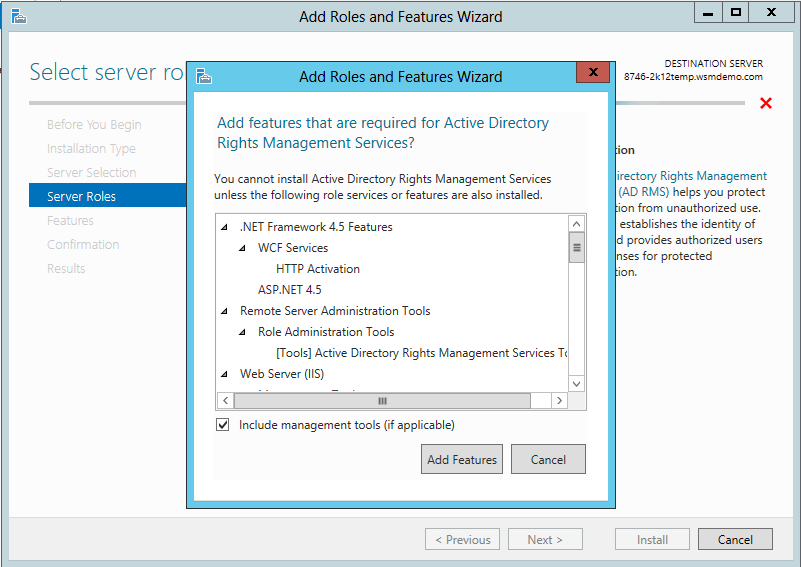
- Click Add Roles and check the Active Directory Rights Management Services box from the list of server roles. Click on Add Required Role Services in the Add Roles Wizard, to proceed and click Next.
- In the left pane, select AD RMS Cluster to create one. Click Next.
- Among the database configuration options, select Use a different database server and specify the sever on which the RMS database is to be hosted. Click on Validate.
- Select Service Account, and select the required Service account and click Next.
- Select Cluster Key Storage and choose the Use AD RMS centrally managed key storage option and enter a Cluster Key Password.
- For Cluster Web Site, choose Default Web Site and click Next.
- For Cluster Address, select Use an SSL-encrypted connection and mention the FQDN and click Validate.
- For Server Authentication Certificate for SSL Encryption, select Choose an existing certificate for SSL encryption and click Import. Retain the default name that appears for the Server Licensor Certificate and proceed by clicking Next.
- Finally, under SCP Registration, choose Register the AD RMS service connection point now option and click Next on the window that follows.
- Click Install on the confirmation page.
The Active Directory Rights Management Services role is now installed on the server.
If you are interested in knowing what’s new in Active Directory Rights Management Services, visit this link.






