Active Directory (AD) schema is a blueprint that describes the rules about the type of objects that can be stored in the AD as well as the attributes related to these objects. The schema thus defines the content, and the structure of the object classes, and the object attributes used to create an object. While creating a new object, the AD references the classes defined in the schema and utilizes the retrieved information to create the object.
Active Directory Schema Components
Objects, classes, and attributes are the building blocks of the schema object definition. Objects are data storage units of Active Directory. A class is a group of object definitions that can be used for object creation in a directory. An attribute is a data item that defines the information in an object or another attribute.
The Active Directory schema stores the class information in a classSchema object and the attribute information in an attributeSchema object. Classes and attributes in a schema are defined using these schema objects. These classes in the schema are used to define objects created in a directory. The schema, however, does not store the actual objects derived from a class.
Active Directory Schema Structure
The Active Directory schema objects are arranged as a hierarchial directory tree, which is divided into directory partitions. The schema has a separate directory partition that enables it to replicate new schema modifications to other domain controllers, before replicating the objects created using the modified schema. This ensures all domain controllers have identical schema. The topmost object of the schema partition can be referenced using the distinguished name cn=schema, cn=configuration, dc=ForestRootDomain. The domain controllers, however, physically store these different partitions in the same database table called Ntds.dit.
The figure below shows the distinction between the physical and the logical location of the schema. The schema and the schema objects are physically located in the schema partition. However, the logical location of the schema container is under the configuration container. The contents of the schema container can be viewed using the AD schema MMC snap-in or ADSI Edit.
Active Directory Schema Extension
A default schema is created on the domain controller while installing Active Directory. The default schema is also updated whenever a new AD schema version is released by Microsoft. However, there could be a situation where one needs to customize the classes or attributes in order to store a new type of information. For example, if your organization feels the need to add a new “passport number” attribute for user objects, Active Directory schema extension enables modification of the existing schema to fit this new information.
In order to create a new type of object, a classSchema object which defines the new class and its attributes needs to be created first. After adding this class to the schema, new objects that reference this class can be created. Similarly, to customize an attribute, a new attributeSchema object that defines the new attribute needs to be created. This attribute then needs to be added to the appropriate class. Schema can be extended only on the schema master by members of the AD schema admins group.
Thus schema is a very important component of AD and its understanding is vital for technicians who use AD. It helps in standardization of data storage in AD and thereby ensures data integrity during various data handling operations of AD. Schema extension is not something that one would perform often. However, it must be done carefully after great amount of planning as schema extensions are permanent. The only way to rollback a schema extension is by restoring the backup of the old schema. Therefore, the decision on who has access to schema must be made very judiciously.
How to Check Current AD Schema Version
Usually, the AD schema is extended to implement an application that requires an extension of the schema such as Microsoft Exchange and Skype for Business. The other primary reason the schema has to be extended is when a new domain controller with a new version of Windows Server is be added.
Before extending the schema, it is required to check the current AD Schema version. To find out the current version of the Active Directory Schema, you can use the following PowerShell script.
Get-ADObject (Get-ADRootDSE).schemaNamingContext -Property objectVersion
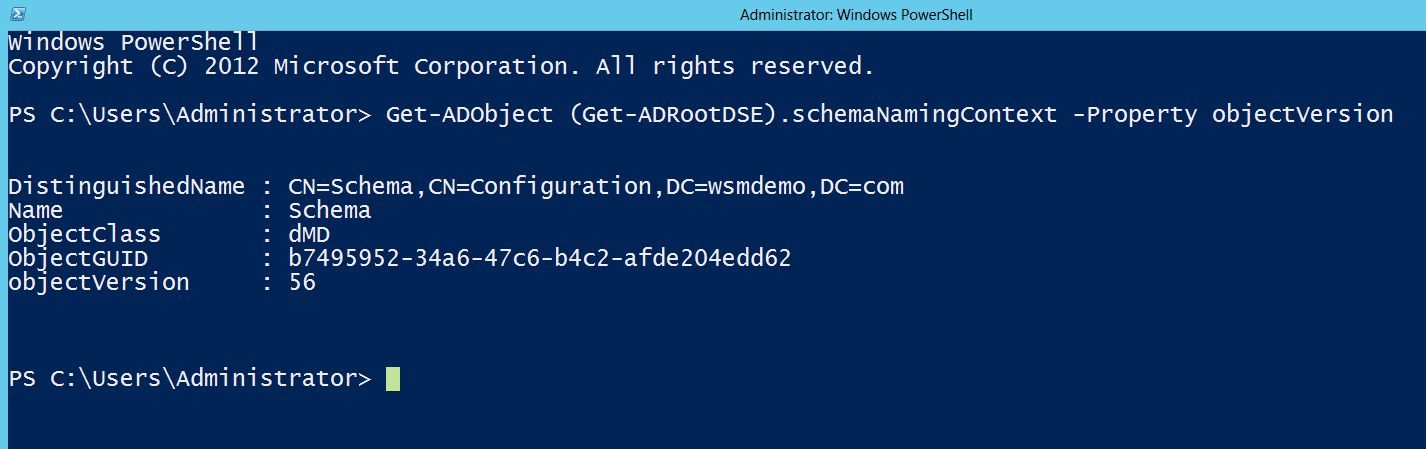
Running the PowerShell script returns an objectVersion value. The following table lists the correspondence between Windows Server versions and versions of the Active Directory Schema.
| Windows Server version | AD Schema objectVersion |
| Windows 2000 | 13 |
| Windows 2003 | 30 |
| Windows 2003 R2 | 31 |
| Windows 2008 | 44 |
| Windows 2008 R2 | 47 |
| Windows 2012 | 56 |
| Windows 2012 R2 | 69 |
| Windows Server 2016 | 87 |
| Windows Server 2019 | 88 |
In our example, the objectVersion returned is 56, so the current Windows Server version is Windows 2012.
Using Command Prompt to check current AD schema version
- Log in to your Active Directory Domain Controller.
- Click Start Menu, right-click Command Prompt, hover over More, and click Run as administrator.
- Run the command dsquery * cn=schema,cn=configuration,dc=<your_domain_name>,dc=<your_domain_suffix> -scope base -attr objectVersion.
- Compare the objectVersion value from the results against the table above. In this case, the objectVersion value is 87, which corresponds to an AD Schema version of Windows Server 2016.
How to Upgrade AD Schema from Windows Server 2012 to Windows Server 2019
In older versions of Windows Server OS such as the Windows Server 2008 R2 and lower, to upgrade to a newer version, you’d have to manually update the forest and the domain schema version. However, with Domain Controllers running Windows Server 2012 and newer, schema can be extended automatically when a new domain controller is added.
The simplest way to update the AD schema version is to install a new server running the Windows Server 2019 version promote it as an additional domain controller. However, it is to be noted that all the changes made to the Schema are irreversible, hence it is highly recommended to maintain a backup of the Windows Server 2008 R2.
- While installing the Windows Server 2019, ensure that the disk size and disk partition are laid out as required.
- When the Windows Server 2019 is installed, promote it as an additional domain controller. Your system may restart multiple times until the new server is promoted as a domain controller (DC).
- Once you’ve established that the your AD is stable after the extension, migrate the Flexible Single Master Operation Roles (FSMO) to the new Windows Server 2019.
- After the FSMO roles are transferred, the Windows Server 2012 has to be demoted. Click on The Manage menu on the main dashboard of Server Manager, and then click Remove Roles and Features
- Click AD DS or All Servers on the navigation pane. Scroll down to the Roles and Features section and then right-click Active Directory Domain Services in the Roles and Features list and click Remove Role or Feature.
- The demoted server can now be decommissioned from the network.






